Spam

Everybody hates it: Spam. Regularly, new surveys show how much money is wasted because company employees have to delete all spam mails. Email is becoming less effective, there is a chance you delete legit mail and you are wasting minutes everyday cleaning your inbox.
How does it work?
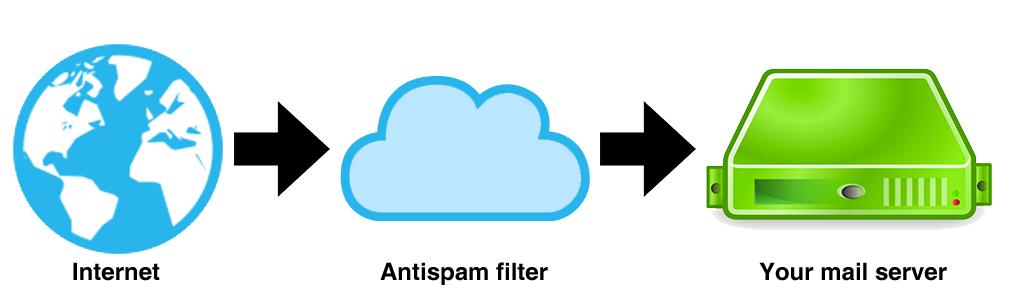
Our spam filter is (virtually) placed in between the sending party and your own mail server. Your e-mail is filtered in the cloud and then forwarded to your mail server. Regardless of the software you run on your own server, this method will always work!
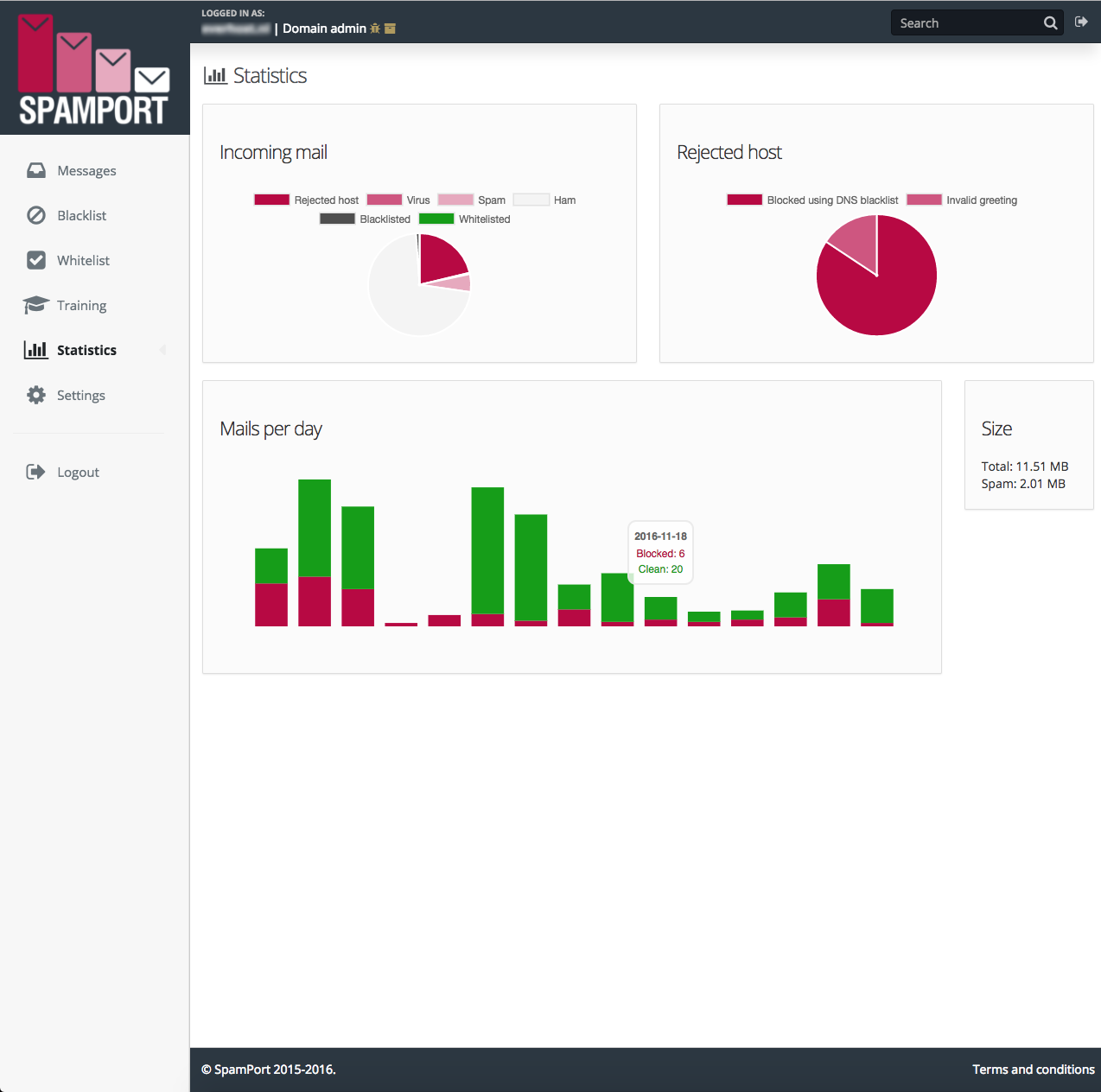
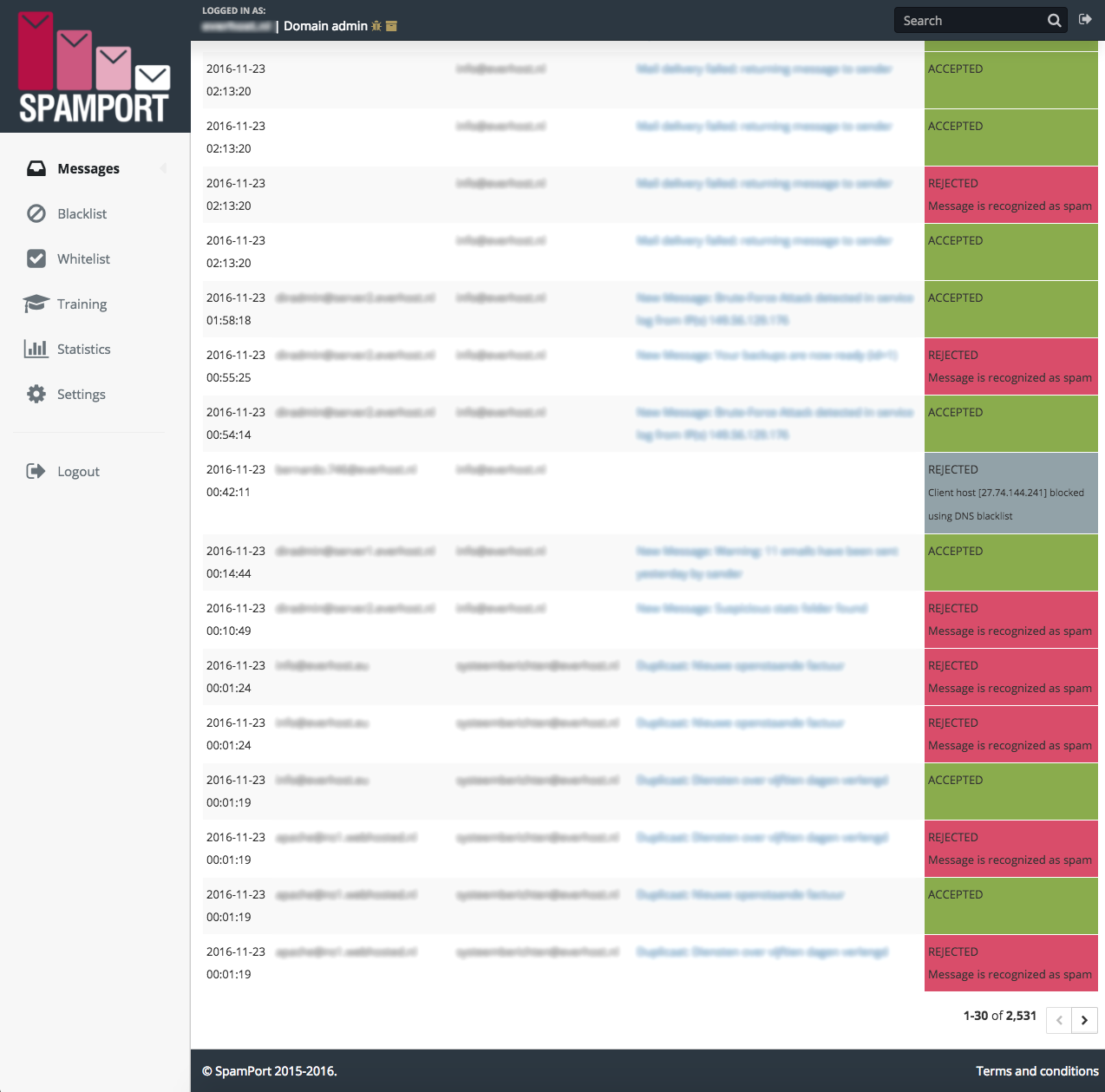
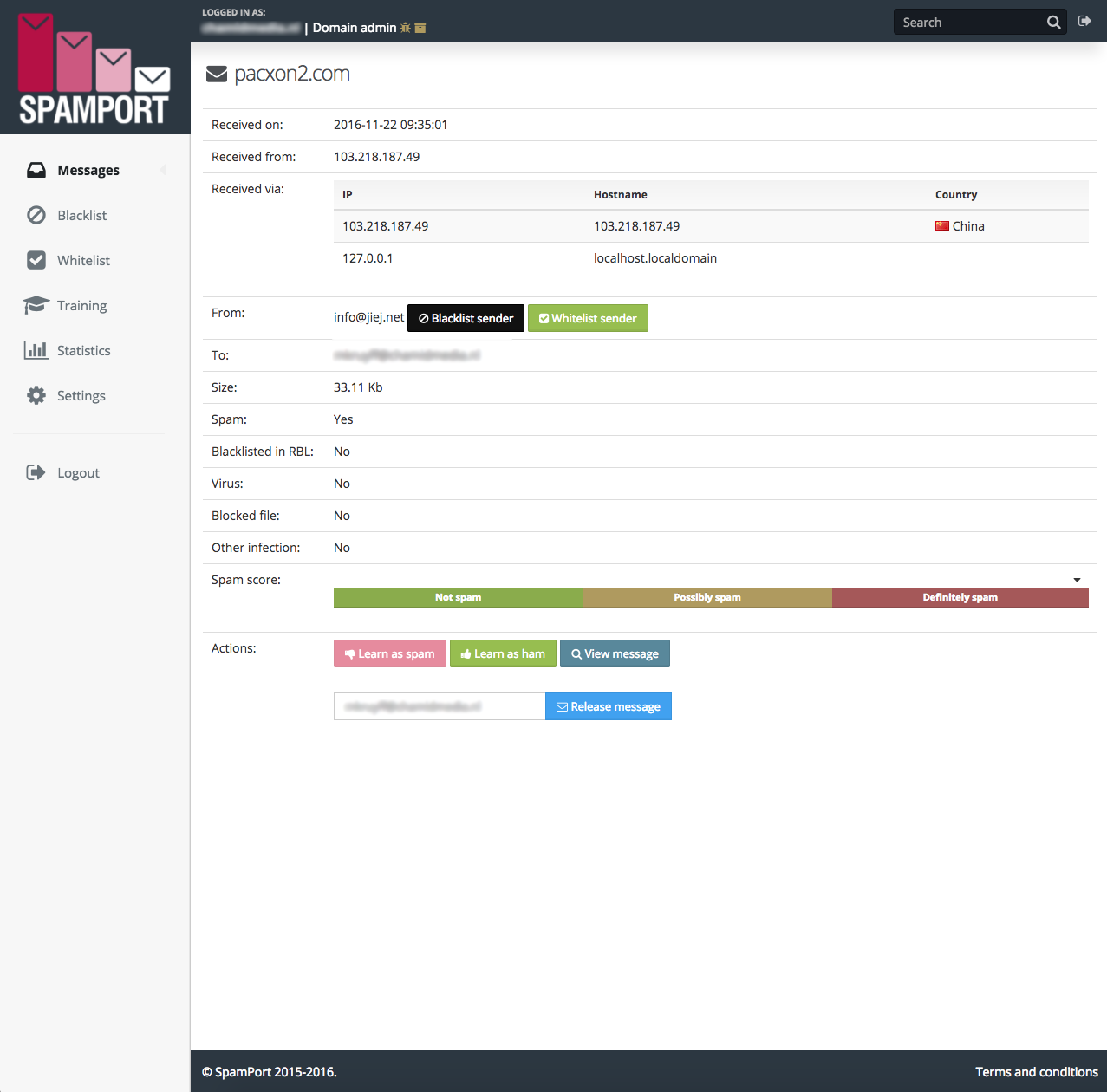
Through the SpamPort control panel, you can easily manage your domain (s) and change settings. It is also possible to release the email. You can also easily make changes in the control panel, to ensure only legit mails reach your inbox.
Email protection for companies and individuals

Our spamfilter blocks 99.98% of all spam and relies on a false-positive ratio of less than 1 in a million. Protect your organisation or personal mailbox from spam, virusses, blacklisting and loss of email. It is possible to see a list of blocked mails and if required, you can make adjustment to the filtering process.
Reduce your costs

The antispam/antivirus filter of SpamPort keeps your mailbox free from spam and virusses. This means, your employees will spend less time cleaning their mailbox and solving malware/virus threats. You don't need to invest in an expensive infrastructure. We will take care of filtering your email without expensive investments.
To use our spamfilter, you don't need a contract. For every domain you wish to use filtering, you can use this service. The spamfilter will be billed yearly.
Filter methods

Blacklisting
The websites and links in the mails are compared against a lost of known and agressive spammers. This list will be combined with the lists that are offered from several antispam organisations.
Score system:
The mail will be scanned and will get a score, based on a list of criteria that spam usually has. When a mail gets a hight score, it will be marked as spam.
Checksum technology:
Central mailservers keep track of mails. They use a checksum technology to trace and follow mails. When too many mails with the same matching checksum pass through, they will be analysed and marked as spam.
Sender check
Checks are done to verify the sender of the mail. For example, we check to see if the mail address is valid. Other complex check investigate the SMTP protocol on a deeper level.
Blacklists/Whitelists:
Users can add trusted mail addresses and IP's to a whitelist. The blacklists works opposite to that.
Spamrun limitation:
DoS-attacks and dictionary attacks (emails using a random mail address) on domains will be blocked.
File attachment limitation
Certain file types, such as .vbl, will be blocked by default.